A west coast-based Healthcare Organization reached out to ITS about advising them on the improvement of the overall efficacy and management of Symantec's endpoint protection infrastructure. It just so happens that ITS employs some of the best Symantec security talent in the industry with senior resources which go back over a decade with the tools and solutions.
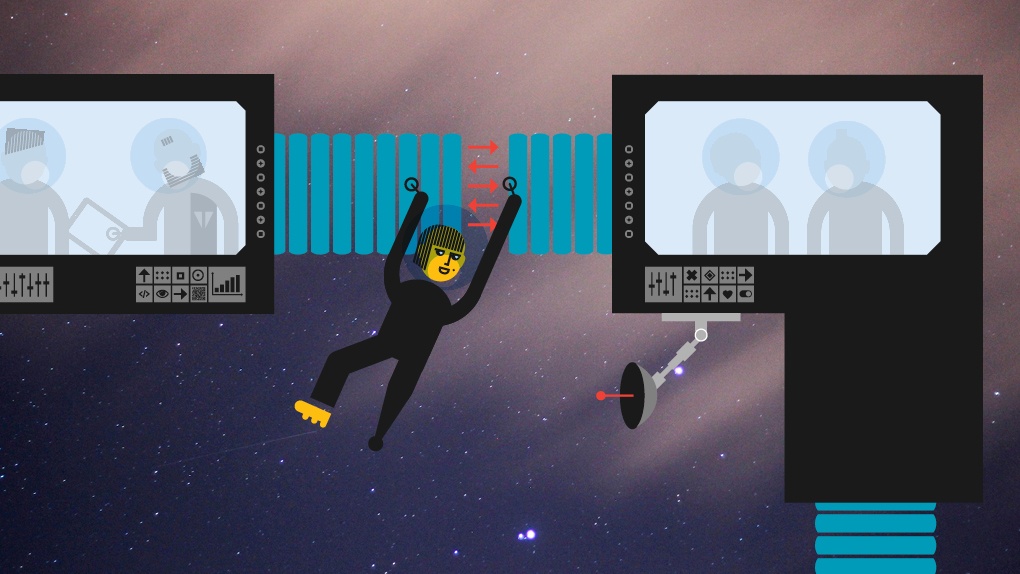
Like many healthcare organizations today, this was a system that had been doing a lot of regional acquisitions and even when these different sites possess the same security toolsets, there are almost always challenges with consistency in protection, in addition to configuration and overall policy management. At the same time, the organization was looking for a solution expert to align the tool to industry and vendor best practices, as there had been configuration drift not only at the main site but inconsistencies at remote sites. Healthcare, in particular, is a vertical experiencing much pressure from cybercriminals through indiscriminate, as well as targeted malware attacks, so this was the utmost priority for them.

During this advisory services engagement, we were able to upgrade them to the latest version, which increased protection with new features like Machine Learning and Generic Exploit Mitigation but was also able to consolidate the management into a design that dramatically improved ease-of-use for the IT and Security Teams.
As the organization continues to grow through future acquisitions, these endpoints can be quickly on-boarded and well protected from known and unknown threats through leveraging the latest technologies, as well as the standardization across all sites and endpoints. The centralized management approach improves management and troubleshooting overall.
A key element to ITS engagement methodology is to transfer as much knowledge as possible to the security teams and analysts responsible for operating and maintaining the solution. This was accomplished throughout the project, with extra attention put toward the engagement close-out. This leaves the customer in a better place with the improvements to the overall protection, but also a staff that is better equipped to manage and troubleshoot day-to-day.
These Stories on SEP