Enterprises are increasingly under threat from sophisticated attacks. In fact, threats dwell in an organization’s environment an average of 190 days!
Security teams also face multiple challenges when attempting to detect and fully expose the extent of an advanced attack. Symantec’s anticipated evolution to full-fledged Endpoint Detection and Response (EDR) is here to address this!
There are a lot of enhancements in this latest version of Symantec's ATP, but we will focus on these five highlights in this video:
- Endpoint Activity Recorder - Continuous visibility across SEP endpoints
- Search, filter and retrieve events for specific endpoints
- File-less threat detection - Detect and view suspicious script and memory exploits
- Hybrid sandboxing - Detonate files on-premises or in the cloud
- Enhanced APIs and integrations with Splunk, ServiceNow, QRadar - Ease custom integrations and leverage pre-built components
Additional comments on the video:
- So this a new product offering VS an upgrade for ATP itself? Both. You can upgrade your existing ATP 8880 to allow you to utilize FDR. The ATP 8840 model.
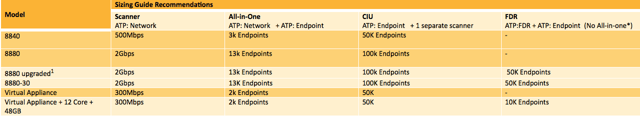
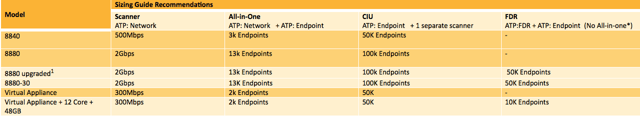
- We deployed the virtual appliance with the recommended system requirements at the time. Does EDR require additional resources? We're currently at 2.3 with 32 GB RAM and 1TB of disk space. Yes. Virtual appliance requires upgrade to 12 cores + 48GB Memory to utilize FDR. See the sizing guide recommendations below.
 The new Recorder feature released in ATP: Endpoint 3.0 requires additional storage, and additional memory is recommended to operate. Existing 8880 (v1 and v2) customers can either:
The new Recorder feature released in ATP: Endpoint 3.0 requires additional storage, and additional memory is recommended to operate. Existing 8880 (v1 and v2) customers can either:
- Use ATP: Endpoint 3.0 without an upgrade using the same feature set available in 2.3
- Upgrade their appliance to support the Recorder capabilities
- The Recorder feature can run on existing HW for demo purposes but is not a supported configuration for production deployments
- A new appliance 8880-30 is already available for sale with the required storage and memory for new customers or existing customers who wish to purchase a new appliance
- Are admin credentials needed to do agent-less scanning? This seems similar to what a Nessus scanner does regarding a credentialed scan. You need access to a share to copy the code to the computer, then access to launch the scripts which would be a local administrator account.

 The new Recorder feature released in ATP: Endpoint 3.0 requires additional storage, and additional memory is recommended to operate. Existing 8880 (v1 and v2) customers can either:
The new Recorder feature released in ATP: Endpoint 3.0 requires additional storage, and additional memory is recommended to operate. Existing 8880 (v1 and v2) customers can either: